Configure LDAP/Kerberos#
Introduction#
LDAP (Lightweight Directory Access Protocol) is a software protocol for enabling anyone in a network to gain access to resources such as files and devices. This tutorial shows an administrator how to configure LDAP authentication.
LDAP need some server configuration before you can enable it from the UI.
Prerequisites#
A server configured with LDAP. See Server Configuration for LDAP for instruction on how to do this.
Step 1: Enable LDAP#
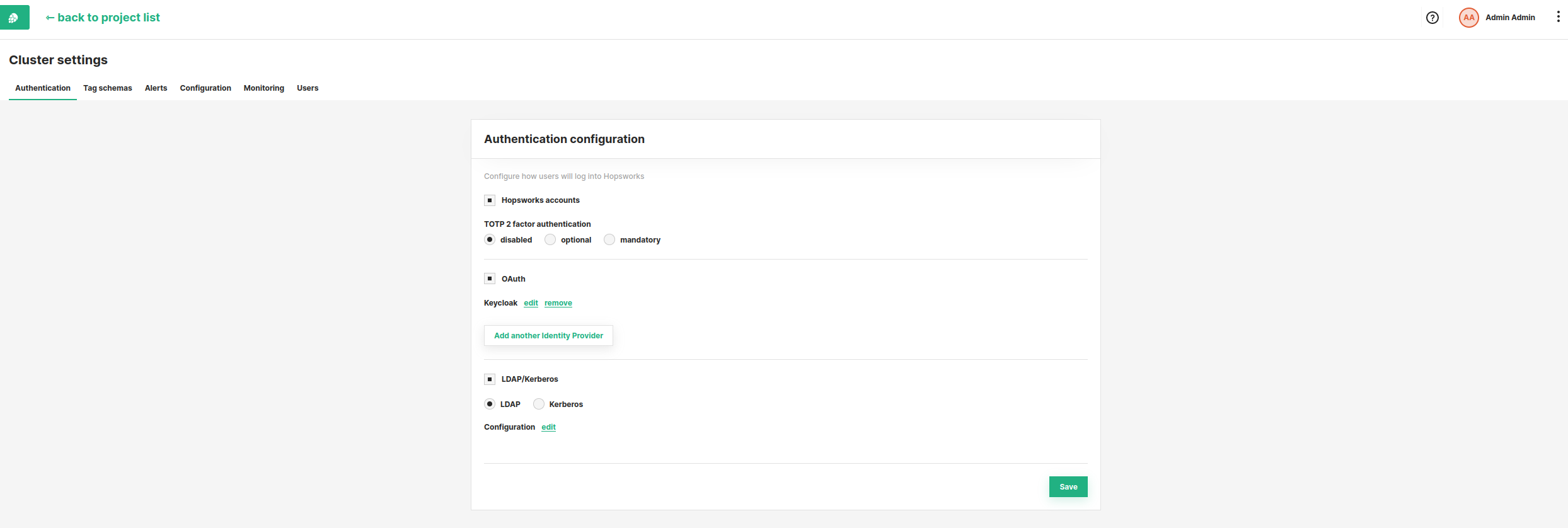
After configuring the server you can configure Authentication methods by clicking on your name in the top right corner of the navigation bar and choosing Cluster Settings from the dropdown menu. In the Authentication tab you can find in Cluster Settings, you can enable LDAP by clicking on the LDAP checkbox.
If LDAP/Kerberos checkbox is not checked make sure that you configured your application server and enable it by clicking on the checkbox.
Step 2: Edit configuration#
Finally, click on edit configuration and fill in the attributes.
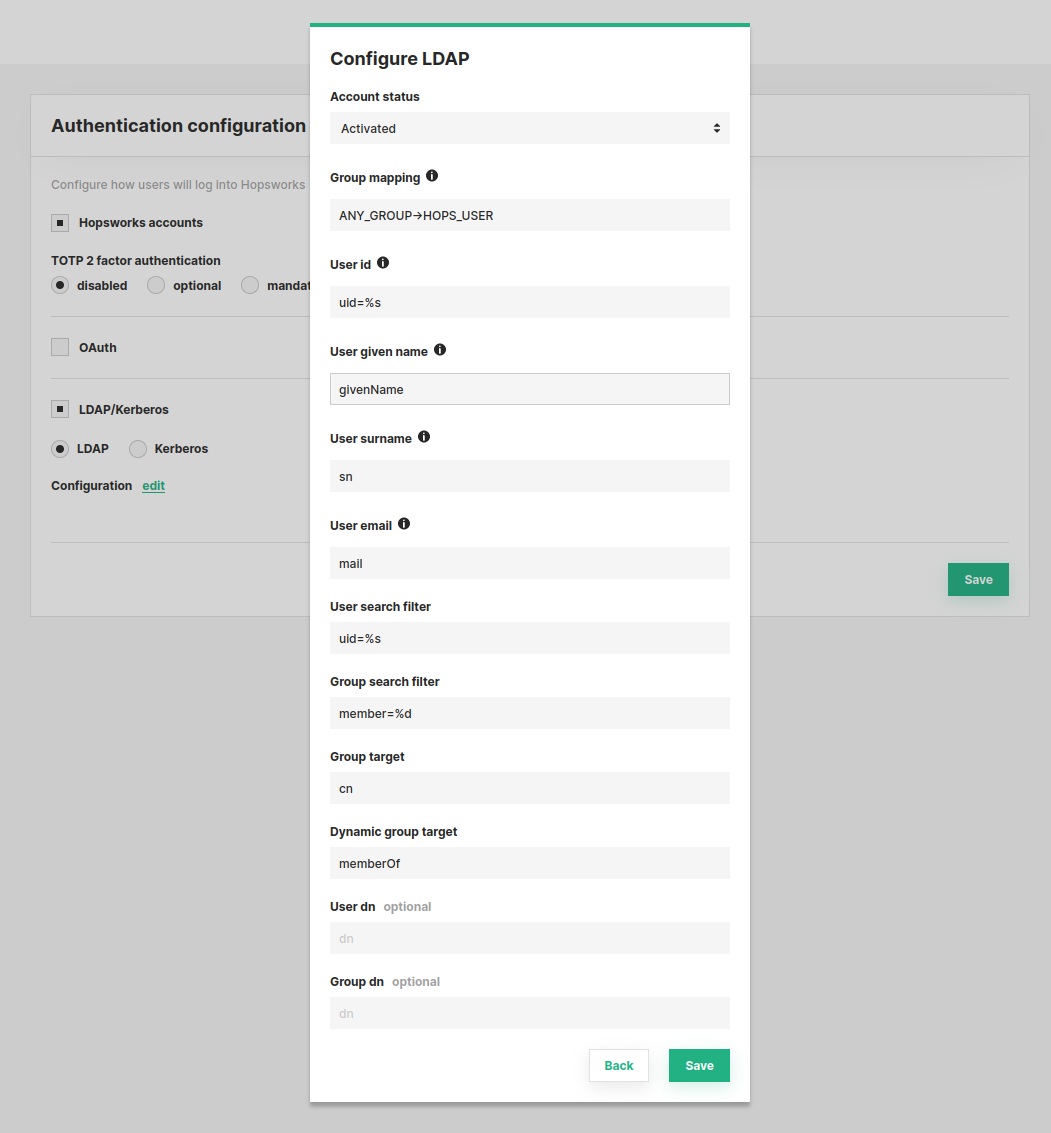
- Account status: the status a user will be assigned when logging in for the first time. If a use is assigned a status different from Activated an admin needs to manually activate each user from the User management.
- Group mapping: allows you to specify a mapping between LDAP groups and Hopsworks groups. The mapping is a semicolon separated string in the form
Directory Administrators->HOPS_ADMIN;IT People-> HOPS_USER. Default is empty. If no mapping is specified, users need to be assigned a role by an admin before they can log in. - User id: the id field in LDAP with a string placeholder. Default
uid=%s. - User given name: the given name field in LDAP. Default
givenName. - User surname: the surname field in LDAP. Default
sn. - User email: the email field in LDAP. Default
mail. - User search filter: the search filter for user. Default
uid=%s. - Group search filter: the search filter for groups. Default
member=%d. - Group target: the target to search for groups in the LDAP directory tree. Default
cn. - Dynamic group target: the target to search for dynamic groups in the LDAP directory tree. Default
memberOf. - User dn: specify the distinguished name (DN) of the container or base point where the users are stored. Default is empty.
- Group dn: specify the DN of the container or base point where the groups are stored. Default is empty.
All defaults are taken from OpenLDAP.
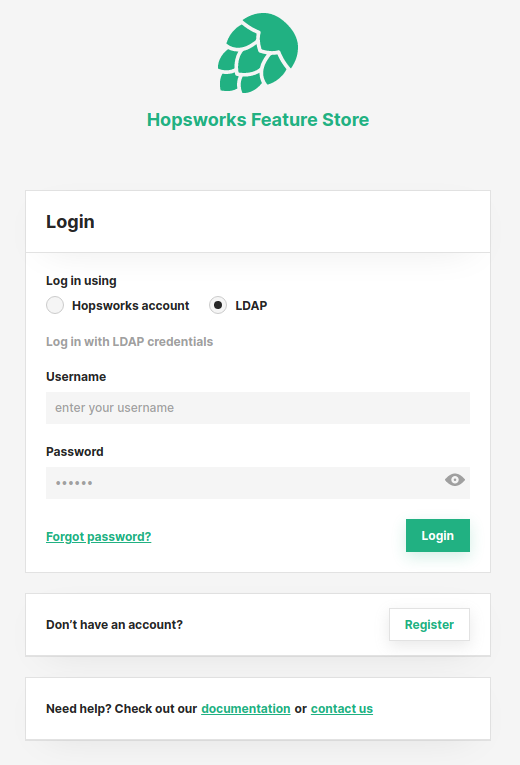
The login page will now have the choice to use LDAP for authentication.
Note
Group mapping can be disabled by setting ldap_group_mapping_enabled=false in the Configuration UI. When group mapping is disabled an administrator needs to activate each user from the User Management page.
If group mapping is disabled then Account status in LDAP configuration above should be set to Verified.
Conclusion#
In this guide you learned how to configure LDAP for authentication.